Why Your Home Cybersecurity is More Important than Ever

During 2020, the home became not just the hub of personal life but of work life as well. As our daily routines were disrupted, our homes turned into full-time schools, cinemas, playgrounds, and workplaces. As the weeks turned into months, TSP Smart Spaces realized that this overnight shift increased risk for our clients. We needed to assess how good our clients’ home cybersecurity was, to make sure that their personal and professional lives were protected from cyber attack.
The home network has frequently been ignored from a cybersecurity standpoint. It’s considered by most employers as a “zero trust” network – just like public WiFi in an airport. But it’s even riskier than public WiFi: if a hacker breaks into your home network, they have 24/7 access for days on end to try to break into your personal and work computers. So we turned to the cybersecurity audit team at TSP IT Services to help us create a solution – one that provides a cyber risk assessment of your home at a reasonable price.
The result is what think is the first comprehensive Cybersecurity Audit for Home product on the market, which focuses on homes of executives and high net worth individuals to ensure that cyber threats are properly evaluated with the rapid shift of working from home.
When we go into an existing smart home to determine how safe a customer’s home is, we look at three primary elements:
- Their network stack
- Existing documentation of their network and smart home automation tech
- Any devices which give outside access to the network – by permission or, worse yet, without permission
Why does cybersecurity matter in a smart home? Or any home for that matter.
For those of us living in large homes, even in the safest neighborhoods, we’ve been used to paying for dependable alarm systems and security companies who monitor our alarms and can respond to break-ins. What are we really protecting in our home? From the standpoint of physical security: maybe some expensive electronics, jewelry, and our personal safety and protection. From a digital security standpoint, the stakes are even higher.
Losing access to bank accounts and financial information can easily cost you tens of thousands of dollars, if not more. In fact, at TSP, we’ve seen successful cybersecurity fraud schemes that have netted criminals over $500,000. And while few worry about personal safety threats over the internet, digital identity theft often has ongoing consequences to the victims.
So, why have so few people paid for cybersecurity audits for the home?
First, there’s never been a service that provides comprehensive business-class cybersecurity audits dedicated for today’s homes. TSP Smart Spaces is one of the first companies to provide a dedicated service for residential homes.
Second, cyber threats don’t feel that real, especially for home users. People don’t report cyber attack damages to their local police as they do with break-ins, so you don’t ever hear of them. But if you talk to someone in cybersecurity insurance or the FBI, the numbers are real. In fact, the FBI saw an increase in over 300% in cyber crime reports during the first wave of the pandemic. Tonya Ugoretz, the deputy assistant director of the FBI’s Cyber Division, said the “rapid shift to telework” had opened up a huge number of cyber vulnerabilities for hackers to exploit.
Third, the amount of high-value transactions on home networks has traditionally been a small fraction of what might be happening on business networks. Most people just figure that hackers will not target the usual home. That changed in 2020, as everyone started to work from home and the amount of critical transactional business shifted dramatically to being mostly work from home.
 of IT professionals think that remote workers pose a greater security risk than on-site workers – OpenVPN
of IT professionals think that remote workers pose a greater security risk than on-site workers – OpenVPN
Even with an alarm system, seldom do the police catch a robbery in progress. But a security system is still essential. Why? Because they work as a deterrent and provide some protection in case of a worst-case that will likely never happen. We need to start thinking about cybersecurity protection for home networks in the same way: as a deterrent and protection against the worst case.
The 3 questions we ask when performing a smart home cybersecurity audit

1. What is in your network stack?
The first generation of smart home dealers came from the world of Hi-Fi – and they didn’t know much about networks. Many of them still don’t. We know that because we frequently see consumer-grade network equipment put in for a $500K smart home system.
As most people found out during the first wave of the pandemic, what matters most isn’t your thousand-dollar speakers but your WiFi and core network. If those aren’t functioning correctly, you have unhappy work-from-home parents and frustrated remote-learning kids. Similarly, in the world of cybersecurity, what keeps your home safe is investing in the core of your network.
First, we look at the installed brands. If your integrator used Linksys or D-link, they opened you up for hacks redirecting you to Coronavirus misinformation. If they used any of the 100,000 Zyxel products out there, they opened you up to backdoors hackers are using every day to penetrate networks.

Remote workers have caused a security breach in 20% of organizations.*
If you have systems by Ruckus, Araknis, or Ubiquiti, you’re in better hands. These are more specialist brands that are generally more secure than consumer brands sold a dime a dozen. But that still doesn’t mean that you’re fully secure. In 2019, a security researcher found three critical vulnerabilities on Ruckus wireless routers that could be used to gain “root” privileges on the router and allowed the attacker unlimited access to the device and the entire network. While Ruckus quickly fixed the vulnerabilities, customers were required to update their devices themselves, a task that may prove too technical for the average user.
Cisco Meraki
TSP recommends networks by Cisco Meraki for our smart homes. Not only is Meraki backed by enterprise security heavyweight Cisco, but it’s also used by some of the most cybersecure organizations in the world, including MIT, Montefiore Hospital, and our client, Accel. Meraki routers include AMP (advanced malware protection) for rapid detection of new and emerging threats. This does more than just prevent users from downloading malware. It “provides comprehensive security before, during, and after a malware attack.”

2. Do you have any network documentation for your home?
I know that for most of us, the idea of having a visual map of your network seems like overkill. Don’t you just plug things into the WiFi router and turn them on?
While that might be the case for the simplest of networks, the houses we work on have different technology scale. In one of our projects, a 3,000 sq-ft home in the Back Bay of Boston, there are over 300 connected devices, with 122 of them having an IP address. Connected devices in a home are part of the Internet of Things (IoT) and pose a serious security risk to your home’s network unless installed correctly. An improperly exposed IoT device can be hacked in as little as 5 minutes, according to NETSCOUT’s Threat Intelligence Report. For a large scale network to be secure, you have to design and plan for scale and growth.
 18% of those surveyed said cybersecurity was not a priority*
18% of those surveyed said cybersecurity was not a priority*
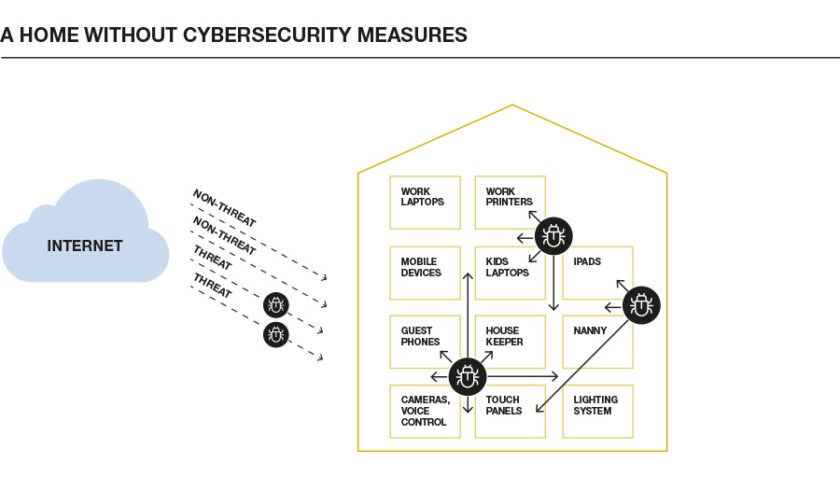
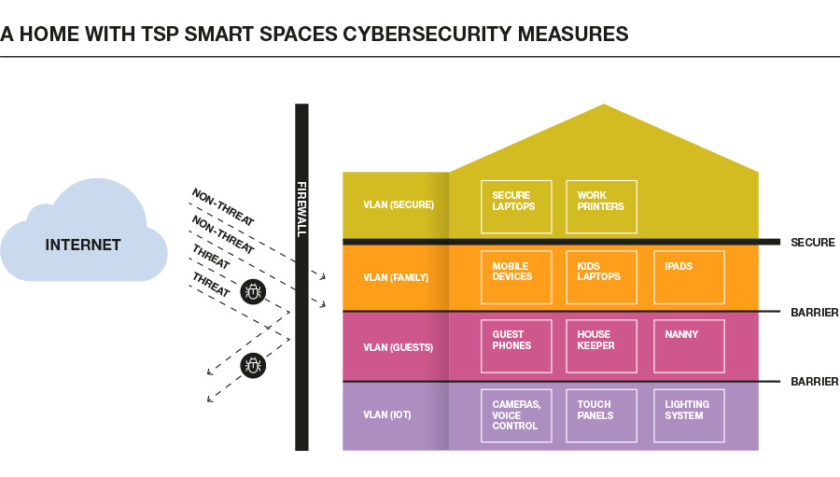
If your smart home doesn’t have any network documentation, then it’s probably not built with cybersecurity in mind. Properly designed networks have multiple “VLANs” (Virtual Local Area Networks) to help protect different classes of devices. These enable groups of devices connected to your network to be partitioned into separate networks. This provides an added layer of network security. Your critical work devices live on a different network from your IoT devices, which are much more vulnerable to attack.
Putting together a secure network requires thought and planning. We ensure that everything is fixed in a way where all of the network traffic is segmented properly and all devices are secure.
3. What outside devices have access to your network?
Finally, we take a look at any devices that might have access to your network outside of your home. These devices could be a maintenance PC installed with remote access software or cloud-based systems IoT devices. Any external device that gains access to your home network poses a security risk. It also provides another entry point for hackers to target your system.
In a recent home cybersecurity audit we performed, we found that a past vendor retained access to the home’s entire network with a single username and password, shared amongst their entire company. While this did not lead to a successful attack, it did pose a major security risk to their home.
Access given to contractors and vendors pose the largest security risk for your home. They offer an easy access point for hackers. This was the case in Target’s $162 million data breach, where hackers gained access to 40 million credit card numbers by stealing credentials from a third-party HVAC vendor to break into its billing platform.
By checking what external devices or people have access to your network and either removing or modifying network permissions for each, we can mitigate the risks to your network posed by these outside sources.
Ensure your home’s cybersecurity
With the Covid-19 pandemic, more and more of us are working from home. Our home networks have become a hub for our personal information and our crucial business information as well. This bypasses the tens of thousands of dollars most businesses put in place with enterprise firewalls. It also leaves business data in the hands of a more vulnerable home network.
TSP Smart Spaces offers business-level cybersecurity protection for your smart home. We also offer award-winning smart home support services. We hold your home network to the same standards as any business network. Not only can we perform an audit of your network, but we can also help to make the changes necessary to protect you and your family from the ever-changing tactics of cyber attackers.
Read more about home network security in this article in Prelude Magazine.